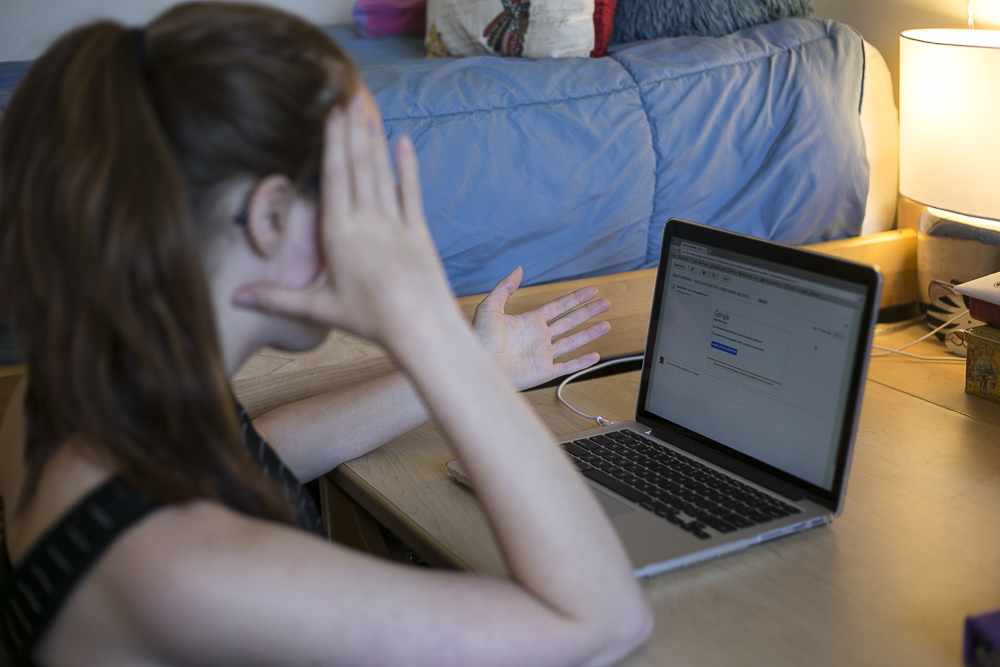
Phishing attacks stand apart from most hacks since they succeed by exploiting trust. Growing up in the heart of Silicon Valley, I know the ease of falling for these malicious emails, as well as the ease in creating them. Copy, paste, modify link and send from a random server. IT tries its best to detect where the emails come from by comparing the real sent location to the expected sent locations. However, that still cannot detect every possible threat. In the face of increasing phishing attacks, it appears timely to impart unto others the knowledge I take for granted: the knowledge of how a hacker thinks.
THE MISSION
According to Timothy 6:10, “the love of money is a root of all kinds of evil.” The methods utilized in cyber phishing parallel real life crime. Identity theft, or stealing account usernames and passwords, mirrors a fraudulent signature. Some phishing attacks also perform a type of cyber blackmailing using personal information in the form of photos, social media account control and any electronic device you frequently use. Traditional monetary theft through the use of a credit or debit card can also act as one possible method. Each method works like a charm, but for any of them to work the hacker needs an account or card number to execute the devious plan.
THE HOW
Phishing, or the technique of sending an email from a trusted source to steal user information, although not the only way to get information, is one of the easiest. Three main methods pervade phishing.
In the first method, the hacker asks for your account information. As the simplest method, the hacker just makes a duplicate website, like myb.iola.edu, asking for a username and password, and once entered, it sends you back to the real website.
The second method involves linking you to a malicious website. Modified websites such as a bad UPS authentication website can “drive by download,” which typically downloads and runs a “keystroke logger.” This stores and sends everything you type from that moment to the hacker who has a filter intended to find usernames and passwords easily.
The third method utilizes malicious attachments. PDFs like a professor’s syllabus can hide auto-running programs which easily run a keystroke logger. Once the PDF is opened it takes every account and card number it wants.
WHAT TO DO
In light of these attacks, we can take four main precautions. First, keep programs like your browser, OS and antivirus software updated because they try their best to identify keystroke loggers or malicious websites before they do any damage. Second, type URL links manually as links can easily send you to the wrong site. Third, get attachments other ways, like through Canvas, Google Drive or Dropbox. Fourth, IT highly recommends enabling the two-step authentication feature for your Biola email account, requiring a hacker to also have a password sent to your phone to log in.
The vigilant survive when others do not, so today I beg of you to act vigilantly with this knowledge. Protect yourself, your friends and your future from the hands of an impersonating, blackmailing thief.